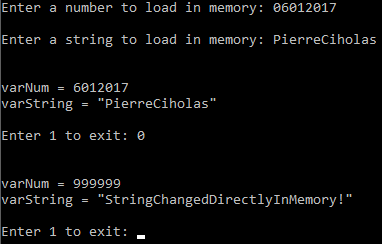
Following my very brief introduction tutorial on how to hack most games with Cheat Engine (in french, sorry) I go a bit further in this post by allowing you to practice with a home made C program. In this post I will show you how to load 2 variables in memory and then modifying them with an external program.
Web searches (Google & Bing) from command line or script
In this post I detail how to perform web searches from command line (linux shell, windows powershell) or in a script in any language (perl, python, etc…). I have tried and compared several tools to do so, using Google and Microsoft Bing and will present them to you. I explore the free solutions and the available API that are free with limitation and allow you to buy credits for more queries. Finally I explore the solutions to limit the number of queries to maximise the efficiency (and possibly stay in the limitation of the free APIs!)
Cloning a disk drive
If you want to clone a disk drive, for example if you switch between a HDD and an SSD, if your old drive has a problem or to clone a full system, you might not want to reinstall everything from scratch even if the destination drive is smaller.
In this post I explain step by step how to do this using only free software and minimum hardware.
Don’t worry (xMind)
In order to improve my organising skills, I am learning to use the free “Mind Mapping” software xMind (www.xmind.net).
Here is my first “Mind Map” :
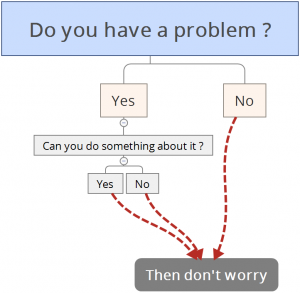
The software is really easy to use, a simple 10 minutes Youtube video will teach you the key concepts and you are good to go!
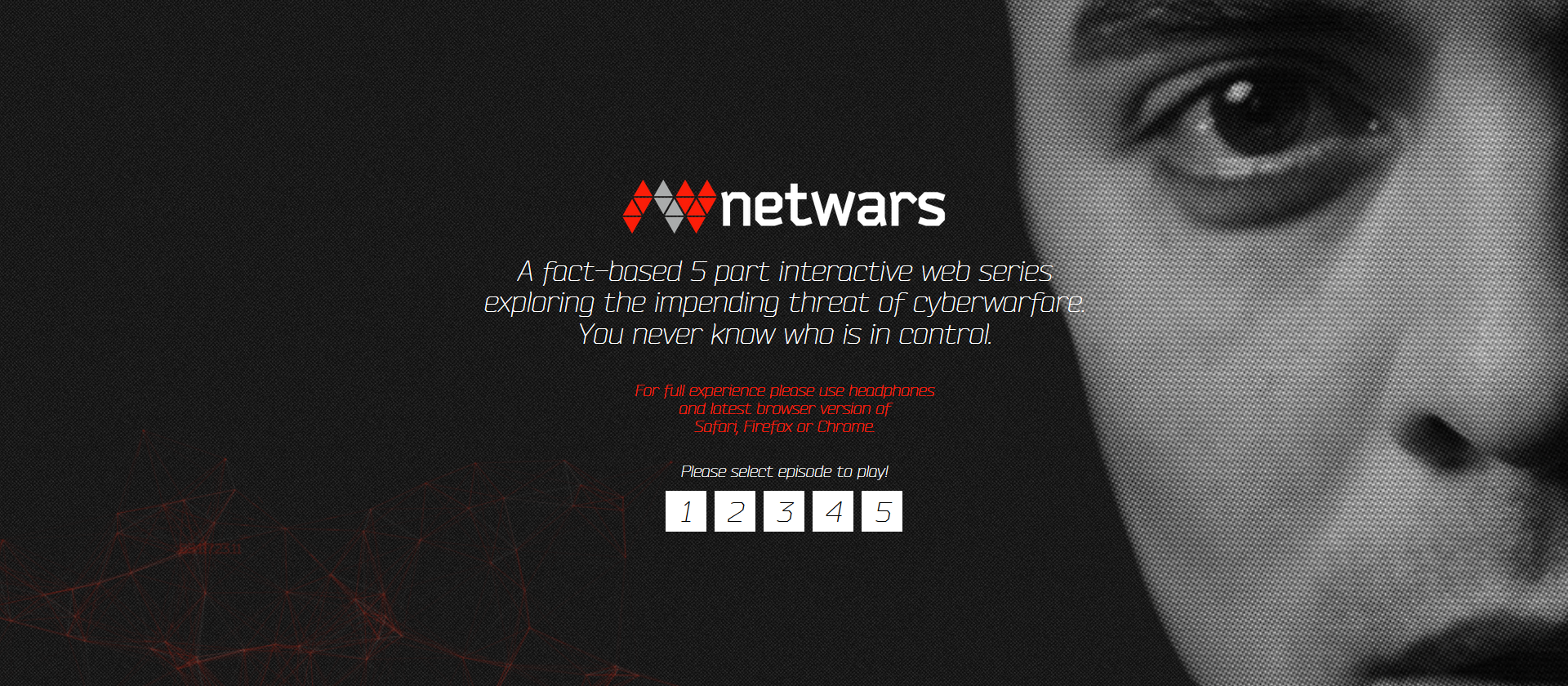
NetWars – Out of CTRL
I suggest you to discover an interactive web documentary.
NetWars – Out of CTRL is a segmented documentary providing interactive phases in order to learn more about IT security and its implications in modern conflicts and geopolitics.
I must warn you that this documentary exploits fear in a machiavellian way and aims a large and unspecialised public.
Watch and learn with this documentary at the following address : http://netwars-project.com/webdoc
Beyond the tale of the two wolves
In every one of us, there is a fight to death between two wolves.
One is evil. He is anger, envy, sorrow, regret, greed, arrogance, self-pity, guilt, resentment, inferiority, lies, false pride, superiority, and ego.
The other is good. He is joy, peace, love, hope, serenity, humility, kindness, benevolence, empathy, generosity, truth and compassion.
The one that will win is the one we feed.
Adapted from a traditional Cherokee tale.
The words are beautiful, the message powerful and we can even feel an impulse while reading it.
This little story is spread and repeated in this form. Simple, powerful and efficient.
However, the true wisdom of this tale lies, to me, in its longer version, by far less known…
Everything is broken, by Quinn Norton
I have translated and adapted in french the excellent article of Quinn Norton, “Everything is broken”.
I think this text is extremely valuable and should be known across languages.
This brilliant summary of the IT security will be a major element in the write up of the first episode of my video serie “A story of magic and technology”, with the author agreement.
I added and modified only minor things to her text, mainly because of the differences between the english and french language, therefore there would be no point in applying the same modifications to the her original publication.
For this reason, I strongly suggest you to read her original text using this link.
Chill out on “You are listening to …”
I found the website www.youarelistening.to providing some good playlist of chillout music (relax ambiant) with on top of it a second audio stream in direct depending on the city you choose.
For example, if you choose the default city, Los Angeles, you will have the LAPD Aero and Special Unit Dispatch radio, for Indianapolis, Indianapolis Metro Police radio and I didn’t look for the other places.
I listen to this when I want to focus, explore the deep web or to lay on the ground, back straight and eyes closed taking long and deep breath (I recommand this to you if you feel stressed, sad, or if you are feeling an overdose of any activity).
Website refurbishment
Hello everyone and thank you for reading me,
I am actually refurbishing the website from scratch and I am about to make new written and video guides, based on my lessons that I have in my english university and on the content of the certification CEH (Certified Ethical Hacker).
These lessons will be longer to write than them of NeoAlpha for those who remember, they will be more structured and better organised.
I hope to be able to make high quality content and share with you my little knowledge about the passion leading me for so many years now : the security of networks and systems.
See you soon!